
SpyHunter 3.10.27
we have the most powerful ANTIVIRUS&SPYWARE AND THE MOST INTERESTING NEWS&ARTICLES ABOUT PC AND THE INTERNET
 PC Security Software: FREE (DOWNLOAD)
PC Security Software: FREE (DOWNLOAD)


LONDON, England (CNN) -- If mention of The Pirate Bay conjures up images of parrots, peg legs and planks, or geeky jargon like BitTorrent and jailbreak leaves you all at sea, this handy A-Z will help you navigate the choppy waters of the online piracy debate.
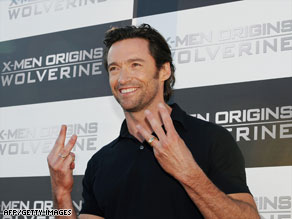
"X-Men Origins: Wolverine," starring Hugh Jackman, was downloaded over a million times after being leaked in early April.
The Screening Room's indispensable lexicon of online piracy will teach you cracking from key generators: You'll never again be caught out wondering how "X-Men Origins: Wolverine" fits into warez.
A is for anti-piracy
Efforts to prevent the illegal transfer and use of copyrighted material -- often spearheaded by corporate associations like the Motion Picture Association of America (MPAA) -- using a variety of digital rights management (DRM) tools like encryption, product keys and serial numbers. Technologically often a step or two behind the pirates, the entertainment industry will sue for breach of copyright.
B is for Bill Gates
As early as 1976, Gates wrote an open letter saying that software piracy could be a problem. Ironically, he has since said that Microsoft actually benefited from piracy in China, where over 90 percent of computers use Windows, most copies of which are pirated. The widespread use of Microsoft's operating system has enabled the software giant to gain pole position in the fast-growing market.
C is for cracking
Modifying software to remove copy protection -- one of the technologies companies use to prevent unauthorized reproduction of media -- to enable the illegal duplication and proliferation of pirated material on disks and online. Mostly done by hackers, not usually for money but to gain respect within the hacker community.
D is for digital rights management (DRM)
Access-control technologies used by manufacturers. Most pirating technology is created to circumvent various types of DRM in order to share copyrighted material online. Apple rid its iTunes library of DRM in early April, but is charging users 30 cents per song to upgrade to DRM-free tracks.
E is for encryption
Originally used by militaries to protect secret message transmissions, encryption allows a user to transform and "lock" information that, upon transfer, can only be opened by a person who has the right "key." Encryption software is one of many anti-piracy measures designed to prevent the spread of copying and transferring copyrighted material.
F is for Free Culture movement
Led by Harvard law professor Lawrence Lessig, the movement believes restrictive copyright laws are strangling humanity's creativity. Under Lessig's "Creative Commons" organization, the movement is advocating for the free copying and modification of creative works -- and rejecting what they perceive to be the culturally oppressive "permission culture" of copyright and intellectual property.
G is for Global Software Piracy
This report by the Business Software Alliance suggested that 35 percent of software installed on PCs worldwide in 2006 was pirated.
H is for hackers
Hackers "wiped," or erased, all the data from the Recording Industry Association of America's (RIAA) Web site in 2008. The incident, which exposed serious flaws in the RIAA's web security, was an embarrassment for the group, which represents the recording industry of the United States.
I is for International Federation of the Phonographic Industry (IFPI)
According to the IFPI's 2008 Digital Music Report, up to 80 percent of data traffic via Internet service providers (ISPs) is involved in the illegal transfer of pirated material.
J is for jailbreak
Mostly commonly associated with the iPhone, it is the practice of downloading illicit software designed to bypass digital rights management, allowing people to upload pirated versions of official iPhone applications for free and use them on their phones.
K is for key generators
Small programs found on pirate sites that allow users to crack open key-locked software like Microsoft Office or Adobe Photoshop by generating valid serial numbers for pirated copies of software that would otherwise only be included with legitimately purchased copies.
L is for Limewire
One of the oldest and most popular peer-to-peer (P2P) file sharing clients, Limewire is a free program used to search for and download pirated content. The program has been accused of having massive security gaps and an abundance of "malware" files, which contain computer viruses that infect users' computers upon completion of a download.
M is for Metallica
The first major band to sue for online music piracy in 2000, Metallica sued file-sharing service, Napster and three U.S. universities for enabling illegal downloading of copyrighted content. The case, which saw the rock group harshly criticized by many of its fans, was eventually settled out of court when Napster agreed to block illegal downloads of the band's songs.
N is for Napster
Online music-sharing service created by a college student in Boston in 1999, which spearheaded the widespread illegal copying and transferring of MP3 music files. A judge shut down the service in 2001. Napster has since relaunched as a legitimate monthly subscription music site.
O is for organized crime
International recording industry organization, IFPI and Interpol say there are links between online piracy and organized crime and terrorism, citing examples from South America to South Africa and Eastern Europe to East Asia.
P is for P2P
More than 20 times as much music is exchanged on peer-to-peer networks as is legally purchased, the Economist magazine wrote in 2008. BitTorrent is a growing P2P technology that allows the rapid downloading of large, multi-gigabyte files.
Q is for quality
According to a survey by the auditor Ernst and Young in India, 66 percent of people believe pirated content is of an inferior quality to the original, but 89 percent say they've used pirated music or films anyway.
R is for R4 card
A $30 Nintendo DS cartridge that can be loaded with hundreds of free, pirated Nintendo games, the R4 card is cheaper than the store price of many single authentic games.
S is for Sweden
Prosecutors in the country filed suit against The Pirate Bay Web site earlier this year for "promoting other people's infringement of copyright laws." Dubbed the "Internet piracy trial of the decade" by UK newspaper The Times, the verdict against the site will have massive implications for the future of online file-sharing, but The Pirate Bay's founders plan to appeal and have previously said that the site will stay up and running.
T is for The Pirate Bay
A very popular file-sharing Web site primarily used as a linking site to find and download pirated movies, music, video games, applications and more. It tracks BitTorrents -- file sharing protocols that enable big, fast file transfers. The Pirate Bay's founders have constantly argued that the Web site does not violate copyright law because the site does not host any copyrighted material, but simply provides a service by indexing the BitTorrents.
U is for Usenet.com
Regarded as a source of much pirated material, this bulletin board site is being sued by the RIAA. Unlike The Pirate Bay, Usenet allows paying customers to download files in a way that is nearly impossible to track. But, like the Swedish site, Usenet has had to defend itself from charges that it encourages its users to violate copyright law.
V is for video games
The Entertainment Software Association says the industry loses $3 billion annually to online piracy.
W is for "Warez"
Slang for any movies, music, applications or any other materials being traded in violation of copyright law.
X is for "X-Men Origins: Wolverine"
A version of the upcoming blockbuster leaked online in March this year, the film has already been downloaded over a million times. The FBI says it is investigating the source of the leak, and the film's star Hugh Jackman has spoken out, calling the leak "a serious crime," and "heartbreaking."
Y is for YouTube
The ubiquitous video site has been sued by major companies like Viacom for publishing and proliferating unauthorized video content online. YouTube has responded by removing copyrighted content, but popular clips of television programs are often reposted by users as soon as they are taken down.
Z is for Zune
Microsoft's answer to the iPod plans to make its entire catalogue of music DRM-free, which will make it even easier to copy and share copyrighted music.
(CNN) -- Internet attacks shut down the social networking site Twitter for about two hours on Thursday morning and caused glitches in other sites like Facebook and LiveJournal, a blogging site.

Some Twitter users expressed near-panic that the site was not working properly Thursday.
It's unclear if the attacks were coordinated against the social media sites.
Twitter says its site's blackout was caused by a "denial of service attack," which likely means a hacker used a herd of infected computers to send bad information to the site to overwhelmed it.
A post to Twitter's blog said its Web site was back online before noon ET, but the site's users still were reporting problems.
"We are continuing to defend against and recover from this attack," the message from the company says.
Facebook and other social networking sites appeared to be affected by Twitter's shut-down, too. Twitter runs applications through those sites and there was speculation that the glitches were related.
"Earlier this morning, we encountered issues within our network that resulted in a short period of degraded site experience for some visitors," said Facebook spokeswoman Kathleen Loughlin.
"No user data was at risk, and the matter is now resolved for the majority of users. We're monitoring the situation to ensure that users continue to have the fast and reliable experience they've come to expect from Facebook," she said.
Twitter's site went down around 9:30 a.m. ET on Thursday and was back online by about 11:30 a.m.
It's unclear who plotted the attack against Twitter and what their motives may have been. Internet attacks sometimes hit Web sites as they become popular. Security experts say financial motives often are behind modern cyber-attacks. Watch Mashable's Adam Ostrow on the Twitter outage ![]()
Twitter -- a micro-blogging site where users post 140-character messages to their followers -- has soared in popularity in recent months. According to comScore, a Web tracking firm, the site had 44 million unique visitors in June.
Thursday's incident highlights the degree to which people depend on online social networks to feel connected to the world.
Some Twitter and Facebook users expressed near-panic that the sites were not working properly. Others reacted with ambivalence.
This is not the first time Twitter has been hit with a cyber-attack. Last month, a hacker broke into the personal Google accounts of Twitter employees, stealing personal information and company financial reports and posting them online.
In an e-mail to CNN.com, Twitter co-founder Biz Stone said that incident is not related to Thursday's security breach.
"There's no indication that this attack is related to any previous activities. We are currently the target of a denial of service attack," Stone said in the e-mail.
"Attacks such as this are malicious efforts orchestrated to disrupt and make unavailable services such as online banks, credit card payment gateways, and in this case, Twitter for intended customers or users. We are defending against this attack now and will continue to update our status blog as we defend and later investigate."
Don DeBolt, director of threat research at CA, a computer security company, said it's too early to tell who or what may be behind the Twitter attack.
But he said denial-of-service attacks target specific Web sites.
"To be effective, [these attacks] need to be focused on a Web site or a series of Web sites," he said. "It's not going to be something where malware (harmful software) is going to be deployed and then randomly attacks Web sites."
John Harrison, a researcher with Web security firm Symantec, said it is very difficult to learn the identity of the attacker, or attackers, as they could be anywhere on Earth and the infected network could span several countries.
Logging on to sites such as Twitter while they are under attack only makes the situation worse because it adds to the overloading of the system, he said.
The U.S. Computer Emergency Readiness Team says it's impossible for Web developers to fully prevent such attacks. But everyday computer users can ensure that their machines aren't used in a coordinated attack like the one seen Thursday.
To protect their computers, consumers should update anti-virus software, create passwords that are difficult to crack and maintain computer firewalls, the agency says.


Guidelines to secure your websites and web servers from being hacked.
Old scripts
Please remember that old installations are an open invitation for hackers. So, if you have installed Joomla or WordPress that you tried out a couple of months ago; please remove it. You should make sure that any script you install on your servers is of the latest version. It takes 5 seconds to hack an old version of Joomla, upload a shell script and have total control over your account.
Passwords
Never use easy to guess passwords or the same password more than once; if someone finds a password of yours they will try it everywhere else until they reach success. If someone finds your webmail password you’re pretty much guaranteed they’ll try it elsewhere – maybe in cPanel, maybe on your online banking!
Cloak Your Folders
You should keep a blank index.html in all of the folders inside your public_html; this will make sure the contents can’t be easily viewed on the internet. CPanel has this function, check out ‘Index Manager’. It’s always a good idea to keep your files and folders secret.
Password Protect Your Admin Folder
You should password protect the admin folder of any scripts you are using, this provides an extra layer of security and is highly recommended. You can do this in cPanel by clicking the Directory Protection link.
So You Got Hacked?
If you got clicked that something has happened, maybe some spam was sent from your account, or you found you were hosting a phishing site, the first step you need to take is changing your passwords. All of them – cPanel, email, site admin passwords, everything.
Next up, go through your web space and remove all old script installations, remember if you installed plugins in your scripts (modules for Joomla/WordPress etc) they can be hacked too! Make sure they’re up-to-date too.
You can check the Error Logs in cPanel for suspicious requests. Generally, a hacker leaves suspicious files around, so look for such files within your public_html folder. Once the files are found, take the details of those files, such as date and time that the file was uploaded, the file name, folder it was in, and inform your web host, so they can check through. Then delete the files.
Being hacked can happen to anyone at all, your security will always depend on its weakest point. If you don’t keep things up-to-date and secure, your site will be hacked and be used for criminal activity in one way or another – however, now is the perfect time to stop this from happening.
